The coronavirus pandemic has accelerated the development of online business, online migration of work flow is faster than ever before. With more and more businesses and consumers relying on E-commerce and online banking to promote innovation and meet the increasing needs of customers, in which cloud native technology has played an vital role, this increase in turn accelerates the popularization of the technique of cloud native.
Gartner expects that by 2022, more than 75% of global enterprises will be running containerized applications in production. More and more practitioners and decision makers have fully recognized the importance of cloud native and are gradually migrating their business applications to the cloud by making in-depth use of cloud-native technology and cloud-native architecture.
As a innovator in the field of artificial intelligence and information security, Starcross Technology is constantly exploring cloud native technology under the guidance of Chinese “new infrastructure” strategy and the “14th Five-Year plan”. In this case, how enterprises cater to the cloud native trend with a better posture? How to implement cloud native? How to build a cloud native infrastructure based on K8s and ensure the platform security and data integrity of K8s cluster? With all these problems, we invited Xu Yue, security expert of Starcross Technology, to share his opinion.

Cloud native —— a foregone conclusion
According to the relevant survey data of the Cloud Security Alliance, China's cloud native industry has reached 35.02 billion yuan in 2019, the value of cloud native technology has achieved a tentative success. Driving by openness and innovation, the cloud native field will continue to reshape the software life cycle and bring continuous value to enterprises.
Xu Yue believed that cloud native is the only path for enterprise to achieve IT infrastructure development and digital transformation. In recent years, especially under the impact of the pandemic, more and more enterprises need to develop agile and resilient online operations in order to adapt to the changing market demand. How to achieve product diversification, how to improve efficiency, how to reduce costs, how to innovate new businesses, and so on. All these mean that enterprises need powerful tools to solve coupling and efficiency problems based on containers. At present, cloud native is experiencing rapid development . Enterprise security teams should not only consider the security of cloud native platform and container infrastructure but also need to design the security protection scheme of application layer for the new business architecture.
Unlock the wisdom of cloud native and promote the innovation of cloud architecture technology
When it comes to cloud native, containers, microservices, DevOps, Serverless have become synonymous with enterprises’ implementation of cloud native, which is also the direction of cloud manufacturers’ layout. Container is the first step of the cloud native revolution, while the container itself actually does not bring value to enterprise directly, but it does not to mean that the container is not important. Run the container on a single machine cannot realize it’s efficiency to the largest extent, only container cluster can maximize the advantages of container, such as good isolation, resource allocation and scheduling management.
Cloud native technology has become ubiquitous because open source frameworks can easily adapt to any use case of enterprises, and Kubernetes is at the forefront of this cloud native technology revolution. Kubernetes (K8s) is an open source system for automating the deployment, expansion, and management of containerized applications. Due to it’s critical function, enterprises utilizing Kubernetes must rely on cloud-native open source to minimize the risk of incompatible code, failed upgrades, and eventual obsoletions.
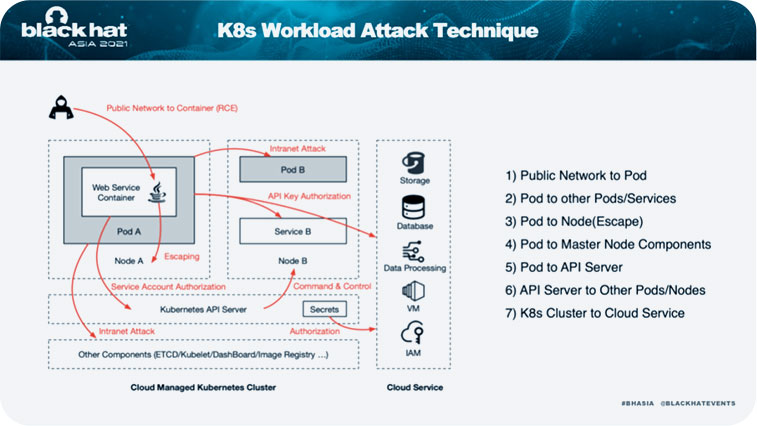
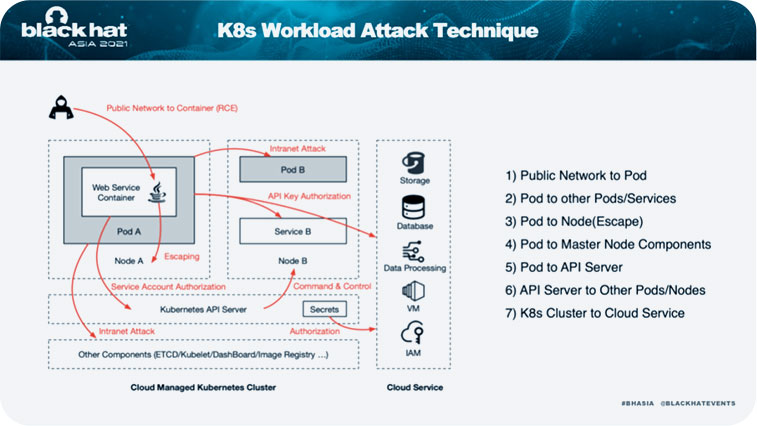
Xu Yue introduced the recent cloud native research results of starcross Technology, namely attack cloud native Kubernetes, he gave a brief introduction to the security test tool, which can help escape from the container and take over the K8s cluster. There are more different attack techniques in K8s environments than in traditional host security. After entering into the container by using application vulnerabilities, we need to the current container position in K8s cluster first, and then use containers escape vulnerability, K8s component vulnerability or permissions control problem to implement further attacks, and we can also find K8s credentials to attack the cloud API service or any other network hosting service, etc.
As for how to facilitate enterprises to make security test of container clusters, the technical team of Starcross Technology gave special consideration to automation by creating a CDK penetration tool, which is written and distributed in binary form. The tool can helps users perform common container detection, Linux post-development, and lateral movement in a K8s cluster.
Focus on the new era and open the door of cloud native
At the recent Black Hat Asia Forum, Starcross Technology made its debut to share the research results of cloud native. Starcross Technology is also invited to introduce it’s new research results on European security conference HITB half a month later. Under the new era, Starcross Technology will actively embrace cloud native and committed to protecting enterprise cloud assets.
At present, under the cloud native era, Starcross Technology will take active innovation, constantly help enterprises to realize cloud migration and win opportunities in the operation to achieve the high efficiency and high income through the cloud native technology.
At last, Xu Yue said that Starcross Technology cloud construction will stick to the latest development trend of cloud native technology, improve public service construction, strengthen operation security and provide open API capabilities to realize the strategic goal of “opening, connecting and enabling”.